A new malware campaign shows how vulnerable IDEs and AI coding agents have become as part of today’s attack surface.
Ongoing Attacks on Developer Environments
Developers are once again being targeted, this time by a self-propagating malware campaign spreading through VS Code extensions.
GlassWorm, discovered by Koi Security, is a malware that exploits the OpenVSX registry, which supplies both standard VS Code IDEs and AI coding assistants like Cursor and Windsurf.
By abusing compromised developer accounts, attackers upload infected extensions that automatically spread to others, turning the IDE into a delivery mechanism.
Propagation Through Compromised Accounts
The GlassWorm campaign propagates through the OpenVSX registry using compromised developer accounts, the first time this has been observed at scale in IDE ecosystems.
The malware scans for developer credentials, npm tokens, and crypto wallets (roughly 49 formats) that can be reused to update npm or extension packages. It hides loader code with invisible Unicode and PUA characters, and its payload updates through Solana blockchain transactions.
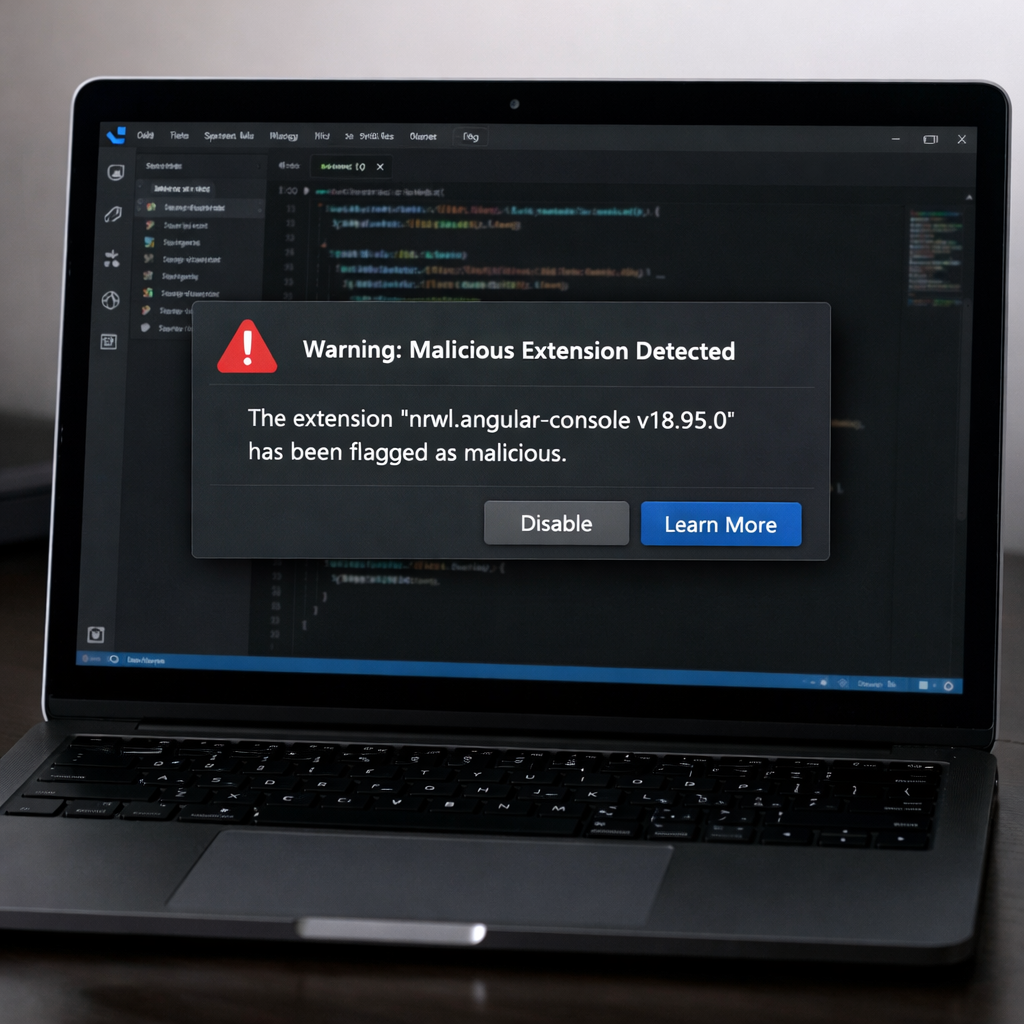
Malicious Extensions Still on the Marketplace
Some compromised extensions remain live on the marketplace even after warnings. One listing even includes a developer’s own disclaimer not to install it, yet it remains available. This persistence shows how weak validation processes in open registries allow malicious uploads to linger.
Reach more about this on our next blog: Open Marketplaces: The Good, the Bad, and The Dangerous
Expanding the Attack Surface
This campaign highlights how developer workstations and AI coding tools have become fully privileged, high-value attack surfaces, the next frontier after browsers and endpoints.
Real-Time Detection with Kirin
In the video below, see how Kirin by Knostic detects an infected extension the moment it’s installed. The user is alerted instantly and guided to remove it, stopping the threat before it spreads.
Learn More
Knostic protects developers and AI coding agents against attacks like these.
Learn more: https://www.getkirin.com/
For practical steps to defend against IDE-targeted malware and protect AI-assisted development, see our blog How to Spot and Analyze Malicious VS Code Extensions
Subscribe to our blog!