LinkedIn’s social algorithms are awful at determining true experts. So what makes one truly an expert? One perspective is the depth of knowledge in a given domain, but the other is one’s ability to organize that knowledge to facilitate the understanding and discovery of new depths.
In my experience of gaining expertise, I have found that having a mental model for understanding is more important than the ability to absorb expert level content. These mental models allow me to organize bits of content into meaningful categories that assist with recall and help me connect the content to the bigger picture.
Most mental models have a one-dimensional structure, usually consisting of a list of categories that simplify our processing of the world around us. These lists are useful, but as we encounter cases that defy available categories, we tend to add more categories. Unfortunately, if we add too many categories, it can make the list less useful and harder for non-experts to understand the bigger picture..
Avoiding this Outcome
One way to avoid this outcome is to add another dimension instead of more categories on the same dimension. This new dimension should ideally be a different mental model that is tangentially connected but mutually exclusive with any other dimensions. The merger of these mental models creates a way to systematically capture more categories and also reveals undiscovered categories.
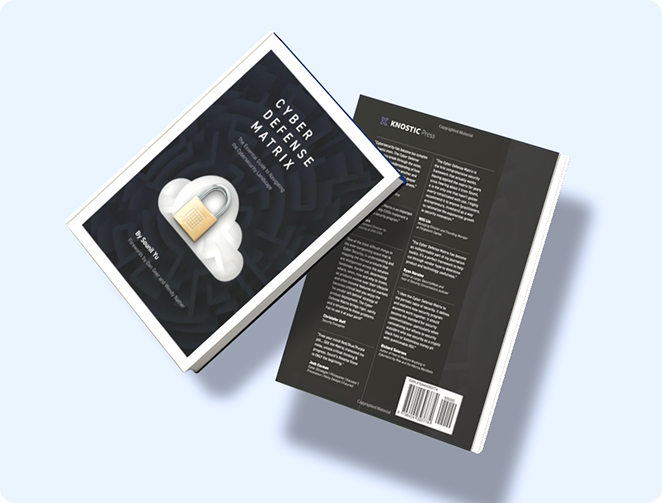
The Cyber Defense Matrix is such an example of the merger of three mental models that adds more structure and thus more depth to our understanding.
- The NIST Cybersecurity Framework: The original five functions of IDENTIFY, PROTECT, DETECT, RESPOND, and RECOVER
- Sounil’s Cyber Asset Model: These are the cyber asset classes of DEVICES, APPLICATIONS, NETWORKS, DATA, and USERS. Adam Shostack once suggested to me that these five asset classes resembles something associated with COBIT, but I’m not sure I have found that association. I haven’t actually found another solid reference for these five asset classes, so I’m happy to claim it for now until someone can point to an established reference.
- Leavitt’s Diamond Model: Originally called Structure, Tasks, PEOPLE, and TECHNOLOGY. Structure and Tasks got combined into PROCESS. I’ve argued that GOVERN establishes structure, and the Cyber Defense Matrix itself is that structure.
However, we can't just add any mental model. There must be some logical overlap among the different models. For the Cyber Defense Matrix, what creates the intersection of the three mental models is actually a hidden mental model.1
The Cyber Defense Matrix
The hidden model that brings the full Cyber Defense Matrix into view is the grammatical sentence construction of interrogative pronouns (who, what, when, where, and how) with a verb and its direct object:
- Interrogative pronouns: PEOPLE (Who); TECHNOLOGY (What); PROCESS (When, Where, How)
- Verbs: IDENTIFY, PROTECT, DETECT, RESPOND, and RECOVER
- Direct Object: DEVICES, APPLICATIONS, NETWORKS, DATA, and USERS
When we combine this sentence structure, the Cyber Defense Matrix allows us to methodically ask the following types of questions:
- [Who are the] PEOPLE [that are responsible for] IDENTIFYing DEVICES?
- [What] TECHNOLOGY [is used to] IDENTIFY DEVICES?
- [When, where, and how, i.e., PROCESS] are the people and technology IDENTIFYing DEVICES?
By applying this same sentence construction for all the boxes of the Cyber Defense Matrix, we can see how the merger of these four mental models establishes most of what is currently referred to as GOVERN in the NIST Cybersecurity Framework.
Starting with a single mental model, it may be challenging initially to find a second model that intersects, but once you merge those two models, the increased surface area of your combined model enables you to easily find more intersecting models. If you can find that overlap and merge mental models, many new discoveries await.
What's Next?
The Cyber Defense Matrix has a large surface area, which affords us the opportunity to merge in many more models. Stay tuned for my next blog where I'll share how other models merge together and the new things we can discover from that merger.
1 There are a few other hidden mental models in the Cyber Defense Matrix, but I won’t cover those now. Maybe later.
Links to the Merging Mental Models series:
Subscribe to our blog!








![AI Data Governance Guide for Enterprise Teams [2025]](https://www.knostic.ai/hs-fs/hubfs/What-is-AI-data-governance.jpg?width=520&height=294&name=What-is-AI-data-governance.jpg)


